Quantum News Briefs June 21: US must maintain its quantum advantage, quantum computing more accessible with cloud-based quantum computers, QKD against future cyberattacks and MORE

Quantum News Briefs opens today with an urgent article from the National Defense journal warning that “The USA must preserve its quantum advantage” followed by an article highlighting the growing accessibility to quantum computing through the cloud, and a discussion of how QKD defends against future cyberattacks. Two research projects also in today’s lineup: Brain imaging research at Aalto University using quantum sensors on cat brains and secondly the use of a trapped-ion computer to measure quantum phases from Duke U and UofMaryland.
*****
U.S. Must Preserve its Quantum Advantage
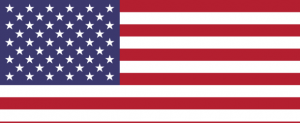 U.S. dependence on technology has become acute, especially with the current maneuvering and positioning by those willing to upset international stability. It is now an imperative to prevent a slow, spiraling descent while potential adversaries ascend. A survey of the sciences that have the potential to shift the paradigm yields a sole area of technical knowledge with enormous implications across the spectrum of commercial and defense: quantum technology. Only the key points from National Defense’s John Johnson’s lengthy warning article are summarized here, but the complete article is worth a read.
U.S. dependence on technology has become acute, especially with the current maneuvering and positioning by those willing to upset international stability. It is now an imperative to prevent a slow, spiraling descent while potential adversaries ascend. A survey of the sciences that have the potential to shift the paradigm yields a sole area of technical knowledge with enormous implications across the spectrum of commercial and defense: quantum technology. Only the key points from National Defense’s John Johnson’s lengthy warning article are summarized here, but the complete article is worth a read.
No longer a laboratory experiment, quantum technology now yields practical applications, but there is irrevocable harm if wielded by contrarians to global order. Encrypted transactions today can be held in depositories by others until such time as quantum computing is able to decipher what we today consider unbreakable code. Intellectual property, classified data and all personal information will be considered “open source” information. The danger is incomprehensible and the very reason for the recent presidential decree.
Safeguarding classified data, intellectual property and personal information is the governments imperative task.
Research and development will continue for decades, but applications are possible now. To date, scientists and research engineers have paced the development, but potential victims such as financial institutions, and defense and medical research organizations cannot stand on the sidelines any longer. The time is now to get involved and contribute to the drive for quantum applications.
*****
Quantum Computing Turns into Accessible Services with the Cloud-Based Quantum Computers
 Quantum cloud computing is a field that emerged with the convergence of quantum computing and cloud computing. Firms such as IBM, Google, Microsoft, and Amazon use quantum computers with cloud computing technologies that a network may access without needing a physical quantum computer. It implies that individuals as basic users will soon be able to utilize quantum computers in the cloud thus making the quantum computing experience more accessible than ever before.
Quantum cloud computing is a field that emerged with the convergence of quantum computing and cloud computing. Firms such as IBM, Google, Microsoft, and Amazon use quantum computers with cloud computing technologies that a network may access without needing a physical quantum computer. It implies that individuals as basic users will soon be able to utilize quantum computers in the cloud thus making the quantum computing experience more accessible than ever before.
Quantum cloud computing allows users to connect directly to emulators, simulators, and quantum processors. Vendors provide programming languages, tools, and documentation for implementing quantum computing applications in various ways.
Businesses and researchers mostly use quantum cloud computing to test their quantum algorithms. Quantum algorithms are initially created on conventional computers and then tested in real quantum computers via the cloud.
Quantum cloud computing connects developers’ conventional computers to the quantum machine image (QMI). QMIs are virtualized programming and execution environments for creating and executing quantum software programs. The programmed code is run on quantum virtual machines (QVMs). QVMs are quantum machines that execute and generate a waveform on quantum processors. The quantum machine image communicates with the quantum processing unit (QPU), a quantum chip with interconnected qubits. Waveforms are used to program these qubits. The data received by the QMIP is processed and transmitted back to the traditional computer through the QPU.
The cloud, despite its flaws, is an excellent method to utilize quantum computing. Quantum computing can achieve great computational performance with little I/O. Cloud companies will be among the first providers of quantum-as-a-service since they have both technological capabilities and a large customer base. They will look for the best software development and deployment stacks. Quantum cloud computing will grow as wide as AI in the next years if some real issues can be overcome.
*****
Brain Imaging Device Based on Quantum Optical Sensors to Characterize Complexity of Temporal Structures in Cat & Dog Brains
 Professor Lauri Parkkonen’s team at Aalto University has been developing quantum optical sensors for measuring the brain’s magnetic fields using a technique known as magnetoencephalography (MEG) for years. In traditional MEG, the superconducting sensors operate at very low temperatures and need centimeters of thermal insulation, but the quantum optical sensors work at room temperature, so they can be placed directly on the surface of the head.
Professor Lauri Parkkonen’s team at Aalto University has been developing quantum optical sensors for measuring the brain’s magnetic fields using a technique known as magnetoencephalography (MEG) for years. In traditional MEG, the superconducting sensors operate at very low temperatures and need centimeters of thermal insulation, but the quantum optical sensors work at room temperature, so they can be placed directly on the surface of the head.
Parkkonen and his team plan to use the new method to build on their earlier work measuring brain activity in cats and dogs. Now they plan to characterize the complexity of the temporal structures in sensory stimuli that cat and dog brains can track. Similar experiments in humans have found that our brain produces specific responses to deviations in complex structures only when we attend to the stimuli and become aware of the deviations. Once the technique is perfected, Parkkonen and his team plan to use it to make similar measurements in human babies.
*****
Trapped-Ion Computer Utilized for Researching Quantum Phases
 Researchers at NIST/University of Maryland and Duke University have recently used a trapped-ion quantum computer to realize two measurement-induced quantum phases, namely the pure phase and mixed or coding phase during a purification phase transition. Their findings contribute to the experimental understanding of many-body quantum systems.
Researchers at NIST/University of Maryland and Duke University have recently used a trapped-ion quantum computer to realize two measurement-induced quantum phases, namely the pure phase and mixed or coding phase during a purification phase transition. Their findings contribute to the experimental understanding of many-body quantum systems.
Using their trapped-ion quantum computer, the team was able to probe both the pure phase of the purification phase transition and the mixed or coding phase. In the first of these states, the system is rapidly projected to a pure state, which is related to the measurement outcomes. In the second, the system’s initial state is partly encoded into a quantum error correcting coding space, which retains the system’s memory of its original conditions for a longer time.
Noel and her colleagues’ successful realization of these two phases of the purification transition in their ion-trap quantum computer could inspire other teams to use similar systems to probe other quantum phases of matter.
“We now plan to continue to study critical phenomena in random circuits using our trapped ion quantum computer. We will add more qubits and mid-circuit measurement to increase the hardware capabilities. We will work to find new observables and interesting transitions that are similar to the one observed here in order to understand more about quantum computing and open quantum systems more generally.”
*****
A Qubit of Solace: How QKD Systems Defend Against Future Cyberattacks
 Quantum key distribution (QKD) is a technique for secure communication that enables two parties to produce a shared random key known only to them, which can then be used to encrypt and decrypt messages. QKD is provably secure against an eavesdropper attempting to copy the and since it does not rely on public-key techniques, removes many attack threats posed by quantum computers against the key exchange. The QKD benefits are rooted in the laws of quantum physics.
Quantum key distribution (QKD) is a technique for secure communication that enables two parties to produce a shared random key known only to them, which can then be used to encrypt and decrypt messages. QKD is provably secure against an eavesdropper attempting to copy the and since it does not rely on public-key techniques, removes many attack threats posed by quantum computers against the key exchange. The QKD benefits are rooted in the laws of quantum physics.
The principle behind a QKD system involves using the measurement of individual photons transmitted through a fiber optic channel to generate shared secret keys that are exchanged and synchronized by a pair of QKD servers. These keys are then used by cryptographic algorithms to encrypt and decrypt the information. The main security benefit behind QKD is the ability of the two communicating parties to detect any attempt to read the quantum state of a photon while it is in the fiber via eavesdropping techniques. Immediately knowing that security has been compromised enables the QKD servers to take appropriate action, including aborting the information exchange, creating a new secure key, routing the information over a different secure link or purposely spoofing the eavesdropper with faulty information.
From a financial services perspective, QKD can be used to securely exchange information in a wide variety of use cases including portfolio optimization, option pricing, risk analysis and numerous applications in the realm of machine learning, ranging from fraud detection to natural language processing.
*****
Sandra K. Helsel, Ph.D. has been researching and reporting on frontier technologies since 1990. She has her Ph.D. from the University of Arizona.