QED: Quantum Ensured Defense of Critical Infrastructure

(Sponsored by Qubitekk, Inc.; Authored by Scott Packard) The life-sustaining critical infrastructure of the United States—power, gas and oil, water distribution, wastewater collection and treatment, and telecommunications networks—is dependent on a critically flawed information security system built upon vulnerable cryptography. This vulnerable cryptography, based on the complex mathematical factorization of integers, faces challenges from advances in computing power, efficient algorithm, and artificial intelligence in the hands of malign actors, hackers, looking to exploit the gaps for monetary gain or strategic advantage. Critical infrastructure protection is not only a life-safety issue—it’s a national security one, as well. Quantum physics offers a solution to this threat – leveraging the unusual phenomena of the quantum realm—by employing single particles of light, photons, to create symmetric cryptographic keys that can be used to lockdown access and control of our infrastructure systems.
Imagine the widespread loss of electric power or natural gas distribution in the northeast United States at the height of winter, or a similar power loss during the dog days of summer in the southeast. People—the elderly, children, the disadvantaged—either freezing without vital heating or roasting absent cooling, would suffer and die in large numbers. The costs in loss of life alone are terrible to consider, but the larger economic losses in productivity and distribution of goods would likely be in the billions of dollars.
Electric Distribution Station
We don’t have to imagine these scenarios—there are several examples ready at hand that demonstrate the dangers inherent in the disruption of critical infrastructure. The loss of power when a winter storm struck Texas in February 2021 affected over 4 million people, with numerous lives lost and economic costs estimated up to $130 billion. When power returned three weeks later, the suffering continued as water treatment facilities serving over 14 million people were forced to issue “boil water” notices due to bursting of frozen water supply and distribution pipes[1].
Similar disruption occurred with the recent cyberattack against the Colonial Oil Pipeline in April 2021[2] when hackers disabled the corporate IT network in a way that affected control of one of the nation’s largest pipelines, carrying refined gasoline and jet fuel in 5,500 miles of pipe from Texas to New York.
This attack brought into stark relief the dependency of our communities and economics upon a network of vulnerable infrastructure. While the Texas power loss was natural event, a cyberattack on the industrial control systems of the electric grid could have produced similar results.
Telecommunications networks have always been a favored target for cyberattacks. Advances in cellular technology, including 5G and NextG, offers new opportunities for mayhem, both for financial gain and military objectives. Many of the systems being purpose-built for 5G networks rely on features of the technology like ultra reliable low-latency communications (URLLC) and massive Machine-Type Communications (mMTC). Automated guided vehicles depend on a consistent, uninterrupted command and control signal and feedback loop. Latency, signal disruption, and spoofing, short of a complete systemic override, would introduce potentially catastrophic variables into systems that require tightly choreographed operations, especially when conducted in close proximity to people.
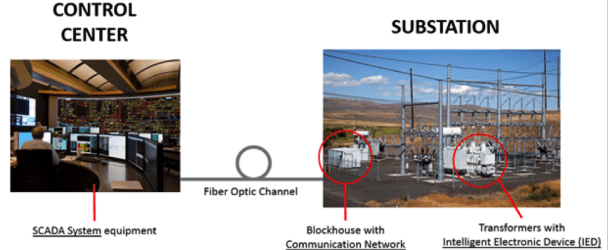
Example of a Smart Substation:
 Most of the national essential infrastructure; electric power, gas and oil distributions, telecommunications; are controlled by computers with safeguards dependent on classical encryption safeguards to protect against unauthorized intrusion. Often touted as “uncrackable,” encryption schemes based on complex mathematical equations are anything but. In 1977, Martin Gardner issued a challenge to decode a “secret” message encrypted with an RSA mechanism, with a prediction that doing so would take a quadrillion years. A team of MIT researchers cracked it 17 years later[3}
Most of the national essential infrastructure; electric power, gas and oil distributions, telecommunications; are controlled by computers with safeguards dependent on classical encryption safeguards to protect against unauthorized intrusion. Often touted as “uncrackable,” encryption schemes based on complex mathematical equations are anything but. In 1977, Martin Gardner issued a challenge to decode a “secret” message encrypted with an RSA mechanism, with a prediction that doing so would take a quadrillion years. A team of MIT researchers cracked it 17 years later[3}
Today’s classical cryptography has advanced such that similar techniques used by the MIT team are no longer effective. However, Gardner’s hubris should serve as a warning against over-dependence on mathematical computation alone. The field of post-quantum computation offers this path, with much promise. But just like existing computational-based cryptography, future advances in cryptography-breaking quantum computers may pose a long-term threat to information security. Quantum physics are not just part of the problem—they also play a part in addressing the threat.
 Photons, individual particles of light, are indivisible, unduplicatable, and leave tell-tale signs of tampering (aka, measuring). Using the quantum mechanical properties of light particles offers a safe, reliable, and secure means of encryption not simply resistant to computational decryption but truly uncrackable. Any networked system presents a vulnerable attack surface.
Photons, individual particles of light, are indivisible, unduplicatable, and leave tell-tale signs of tampering (aka, measuring). Using the quantum mechanical properties of light particles offers a safe, reliable, and secure means of encryption not simply resistant to computational decryption but truly uncrackable. Any networked system presents a vulnerable attack surface.

The real-world application of quantum protected network security in the award-winning collaboration between Los Alamos National Laboratory, Oak Ridge National Laboratory, Chattanooga’s EPB, and Qubitekk demonstrates the commercial viability of quantum technology for the security of connected critical infrastructure systems. While the testbed, Quantum-Ensured Defense of the Smart Electric Grid (QED), was applied to securing an existing electric grid infrastructure in a manner that validates metropolitan-scale quantum communications, the compatibility with other networked critical infrastructure; e.g., gas and oil distribution, broadband internet, telecommunications architecture including 5G cellular networks, makes it a viable quantum solution to a classical problem.
Quantum protection of critical infrastructure control systems is quickly becoming one of the most useful early applications of quantum technology. While quantum computing promises to change the fields of molecular biology, materials science, and machine learning/artificial intelligence some day, today quantum-derived security can bring a level of protection currently unmatched by current classical encryption methods. Demonstrated with a conventional electric grid system, similar methods are be used in other infrastructure testbed.
For more on the topic of using quantum protection to secure communication infrastructure, join Qubitekk’s President and Chief Technology Officer, Dr. Duncan Earl, Thursday, 4 November from 2:00 pm to 2:30 pm, in the panel discussion: Opportunities for the Data Networking and Telephone Industries in the Quantum Internet.
[1] Atkins, Derek; Graff, Michael; Lenstra, Arjen K.; Leyland, Paul C. (1994). The Magic Words are Squeamish Ossifrage. Proceedings of Asiacrypt ’94. Springer-Verlag. pp. 263–277. doi:10.1007/BFb0000440. ISBN 978-3-540-59339-3.
[1] https://www.nytimes.com/2021/05/08/us/politics/cyberattack-colonial-pipeline.html
[2] https://www.foxnews.com/us/14m-texas-residents-still-under-boil-water-notices-as-tens- of-thousands-lack-running-water
[3] Atkins, Derek; Graff, Michael; Lenstra, Arjen K.; Leyland, Paul C. (1994). The Magic Words are Squeamish Ossifrage. Proceedings of Asiacrypt ’94. Springer-Verlag. pp. 263–277. doi:10.1007/BFb0000440. ISBN 978-3-540-59339-3.